 EBRACH, Germany, March 31, 2026 – Machdyne, a pioneer in long-term storage solutions, today announced the launch of FERRIT, a digital archival platform designed to preserve critical information for centuries. Engineered with radiation-resistant F-RAM (ferroelectric RAM) technology, FERRIT delivers unparalleled reliability for institutions and organizations that manage critical data.
EBRACH, Germany, March 31, 2026 – Machdyne, a pioneer in long-term storage solutions, today announced the launch of FERRIT, a digital archival platform designed to preserve critical information for centuries. Engineered with radiation-resistant F-RAM (ferroelectric RAM) technology, FERRIT delivers unparalleled reliability for institutions and organizations that manage critical data.
As part of the launch, Machdyne is opening a pilot program for early adopters, giving select organizations the opportunity to integrate FERRIT systems and help shape the next generation of century-scale digital archival solutions.
“Most storage systems are designed for capacity,” said the founder of Machdyne. “FERRIT was designed to preserve the most important information reliably for centuries.”
FERRIT Key Features
- Century-Scale – Preserves data for up to 200 years, far beyond conventional storage media.
- Fast Writes – Supports a virtually unlimited number of writes, unlike tape or optical media.
- Radiation-Resistant – Maintains data integrity in high-radiation environments.
- Modular – Systems range from 8 MB to 256 MB, providing right-sized protection for essential datasets.
- Compatible – Appears as a USB-C mass storage device, requires no special software, and integrates seamlessly into existing workflows.
- Auditable – Fully open-source designs enable independent verification and auditing.
- Mission-Critical – Ideal for critical documentation, historical records, cryptographic key storage, and archival collections.
The FERRIT platform is being deployed in pilot programs with select institutions in order to demonstrate its reliability, modularity, and ease of integration into existing archival and information management workflows.
Organizations interested in joining the FERRIT pilot program can learn more at machdyne.com/ferrit.
About Machdyne
Machdyne UG is a German electronics manufacturer specializing in long-term digital preservation and resilient computing solutions.

 Survival is the ability to exist in the future.
Survival is the ability to exist in the future.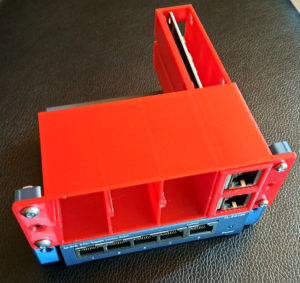

 There doesn’t appear to be anything supernatural about recent advances in AI. Despite the hype, and despite being impressive, it’s still completely understandable, at some level, by humans. In that sense, it may not seem exactly like the AI of science fiction.
There doesn’t appear to be anything supernatural about recent advances in AI. Despite the hype, and despite being impressive, it’s still completely understandable, at some level, by humans. In that sense, it may not seem exactly like the AI of science fiction. Zwölf is an
Zwölf is an 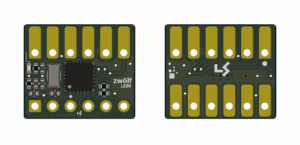
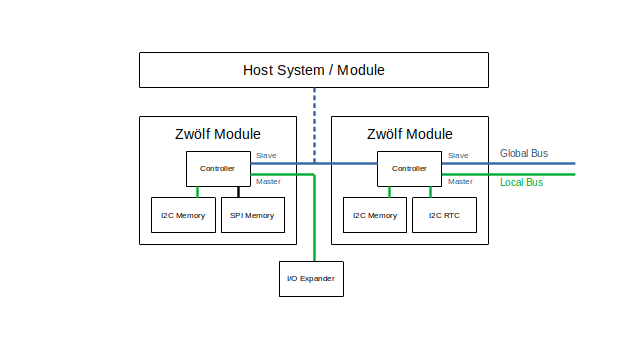
 In order to make our
In order to make our  For quite a while now we’ve wanted to set up a forum for our customers to communicate and share ideas with each other. We tried a few different things but nothing felt quite right. We’re excited to announce a new experiment that we hope our community will find useful: Machdyne
For quite a while now we’ve wanted to set up a forum for our customers to communicate and share ideas with each other. We tried a few different things but nothing felt quite right. We’re excited to announce a new experiment that we hope our community will find useful: Machdyne  In order to make our products more available and affordable we’ve begun to experiment with outsourcing the assembly of certain PCBs.
In order to make our products more available and affordable we’ve begun to experiment with outsourcing the assembly of certain PCBs. One of the goals of Machdyne is to create
One of the goals of Machdyne is to create  We think that
We think that 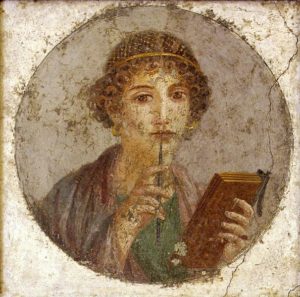 Deep thinking often requires writing. The writing down of thoughts can be affected by perceived privacy. Thus, the erosion of perceived privacy may reduce the capacity for deep thought.
Deep thinking often requires writing. The writing down of thoughts can be affected by perceived privacy. Thus, the erosion of perceived privacy may reduce the capacity for deep thought.